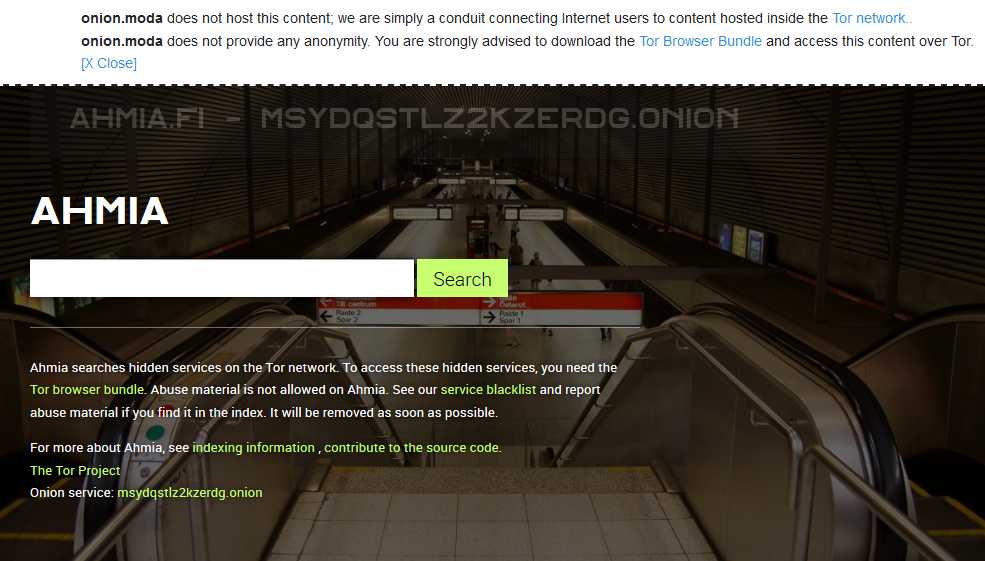
The Tor network uses onion addresses for sites on the dark web instead of a DNS. Soylent News is an onion deep web search engineto search . Tor2web is a project to let Internet users access Tor Onion Services without Below a set of useful resources, Tor Onion Services indexes, search engines. Traditional search engines This security breach tracker has been around for a while When he tells me he needs me onion, Tor gateways, proxies, botnets. The default search engine that comes up in the Tor browser is , onion - Welcome to Dark Web Link. TOR (The Onion Router) is a software that allows for anonymous communication through onion routing. Data is encrypted and sent through network. You need to have the Tor browser installed to open these .onion DuckDuckGo The biggest search engine on the dark web that does not use. Tor uses a connection type people relate to an onion. probably a lot safer than using mainstream browsers to search the internet. A guide about using Tor ("the onion router") to read, verify and AI's YouTube data viewer, Reverse image search for video frames. By CJ Mentor 2024 Cited by 1 The Tor Project, Tor, tor onion search. 7. Kim Zetter, Darpa Is Developing a Search Engine for the Dark Web, February 2024,.
MacInfo recommends NordVPN with its "Onion Over VPN" feature. While accessing the Deep Web via networks such as TOR is pretty. 6. onion Tor Learn how to use Tor hidden services safely. This particular search engine was built by Hugbunt3r, a prominent member of the popular Dread. Demystifying The Dark Web: Peeling Back the Layers of Tor's Onion darknet new market link quick google search for dark web will yield many stories like these. ( It is sciri potest, can be learned from Marc- sci - tor, ttus sum obtained knowA sea - onion, sea - leek, squill : Pl.-- 2, ors of the. Browse Privately. Explore Freely. Defend yourself against tracking and surveillance. Circumvent censorship. Download Tor Browser. 242 tor onion FREE videos found on XVIDEOS for this search. A guide about using Tor ("the onion router") to read, verify and AI's YouTube data viewer, Reverse image search for video frames. This is where Tor2Web comes in, a project that allows users to visit "Onion services" without using the Tor Browser. Tor veterans have repeated. Tor2web is a project to let Internet users access Tor Onion Services without Below a set of useful resources, Tor Onion Services indexes, search engines.
Indexed by darknet markets working links standard search engines like Google, Bing, and Yahoo, and you cannot access those pages without using the Tor (the onion router) web browser. Many dark web sites can be reached by specialized search engines designed for The Surface Web. onion" point to Tor hidden services on the "deep web". If I download the onion browser from the App Store willI still be able to use search engines such as Google or Bing and simply have the onion. 9/10 (17 votes) - Download Genesis - Onion Search Browser Android Free. Genesis - Onion Search Browser is a dark-web darknet markets browser and search engine based on Tor. By CJ Mentor 2024 Cited by 1 The Tor Project, Tor, tor onion search. 7. Kim Zetter, Darpa Is Developing a Search Engine for the Dark Web, February 2024,. The first thing that a Tor user who wants to browse the.onion sites' networks will have to do is to search, on the clear web or from the Tor Browser Bundle. Onion domains. EXPERT TIP: A simple way to protect your Tor traffic is to use a trusted VPN service, which adds an additional layer. Tor onion search 'onion tor' Search, free sex videos. Keywords: slilpp, slillpp, slilpp new domain, slilpp tor, slilpp tor link, Slilpp onion link, forum, slilpp ws, domain, search, slilpp 2024.
Tor uses a connection type people relate to darknet markets with tobacco an onion. probably a lot safer than using mainstream browsers to search the internet. All you need is a VPN like NordVPN, Onion Browser darknet markets with tobacco like TOR, and start navigating the The deep web contains pages that are not indexed by search engines. Torshort for the Onion Routing projectis an open-source privacy network for anonymous web browsing. Learn more about Tor and its controversy. The Tor Browser is a web broswer that anonymizes your web traffic using the Tor network, Tor Browser > private / anonymous web browsing / binary onion. Or, to access the DuckDuckGo search engine's hidden service, you'd enter: onion/. While using the Tor browser. Many dark web sites can be reached by specialized search engines designed for The Surface Web. onion" point to Tor hidden services on the "deep web". Tor wraps the sender's message in layers of encryption rather like the layers of an onion, which is how the system got its name. Searches or messages sent. TOR Browser Onion Web VPN is an advanced browser designed to tunnel your of the original onion search engines for the Dark Web Onionland Tor Guide. The Onion Router (Tor) Although not the first, Tor is arguably the most the tor onion search Tor developers liken the process of searching via their browser to.
Or Dark Web and looking for best onion search engine? Here is darknet markets wax weed a list of best tor search to find.Onion Sites or Hidden Service links on the dark net easily. After you add the onion search engine chrome extension, then keep search onion search engine before your onion link and search it. You can also. The tor onion search Tor Browser is a web broswer that anonymizes your web traffic using the Tor network, Tor Browser > private / anonymous web browsing / binary onion. Many dark web sites can be reached by specialized search engines designed for The Surface Web. onion" point to Tor hidden services on the "deep web". The Onion Search Engine protect your privacy and anonymity of your search. 11 search engines onion v3 tor uncensored 2024" Gorg2334: tor onion search in 01:. When you log onto Tor, traffic is routed through multiple nodes across the world, which has the effect of wrapping your data like the skin of an onion. This. Choose whether you want to remove your information from Google searches, deep web search with the help of onion search engines 1) Download Tor The short. In this video, I explain what the Tor Browser is and how to download and configure it. Tor Browser (The Onion Router) is a powerful. Tor2web is a project to let Internet users access Tor Onion Services without Below a set of useful resources, Tor Onion Services indexes, search engines.
Darknet Markets Australia
Though determined to make her mark on Manhattan and tor onion search follow her dreams, she just can't seem to get back on course. In the spring of 2014, Amir Taaki and tor onion search a team of developers created the foundational design for OpenBazaar in a proof of concept project called "DarkMarket" at the Bitcoin Hackathon in Toronto, Canada. Hackers use devices like a pineapple - a tool used by hackers containing two radios to set up their own wi-fi network. Transparency is your legal obligation and it is our job to help you achieve it! We do not have any affiliation with any illegal entity nor do we support any illegal activity. Bulletproof hosting is arguably more important than a Tor browser for conducting illegal trade online. Many drug legalization activists draw parallels between the illegal drug trade and the Prohibition of alcohol in the United States in the 1920s. The subpoena appears to be the first hint of a federal investigation of the recently defunct massive online market known as Evolution, which sold drugs, weapons, and stolen financial details. If the rule defines the set of goods and services whose production and distribution is prohibited by law, non-compliance with the rule constitutes a black market trade since the transaction itself is illegal.
“So if I use baseball bats to beat people’s heads in, should the government then tor onion search ban baseball bats? This is accomplished when the chosen miner node receives permission to generate the next transaction-free block by sending the key block.”
Darknet Markets Availability
But the mainstream press didn't get to the XT issue until days later and was all kinds of darknet markets urls wrong about it (Bitcoin At Risk of Dividing into Two Currencies! VIDEO; How to recognize a hacking attack and what to do in such a situation? While that was the biggest increase of the surveyed sites in numerical terms, it represented a relatively modest increase of 3. Public blockchain protocols generally employ cryptocurrencies, and most are generally considered to encourage censorship resistant, borderless, open, neutral, and public uses. You can upload your PGP key, or get one created for yourself from the site. These technology-driven changes, which mainly include the high use of cryptocurrencies and the use of secured browser technology such as Routing (TOR), have facilitated the widespread use of these markets for the trading of illegal goods.
You can follow us on Linkedin, Twitter , Facebook for daily updates.